VERA Spoofing PalmVein
Description
All the attacks have been recorded using the same open palm vein sensor used to record the Idiap Research Institute VERA Palmvein Database.
Images are labeled as follow: ID_hand_session_shot.png where "ID" is a 3 digits number that stands for client's ID, "hand" stands for the considered hand which can be "R" or "L" ("Right" or "Left"), and "session" stands for the considered session number which can be "1" or "2" (2 session per hand), and finally, "shot" stands for the considered shot number which can be "1" to "5" (5 shots per palm).
Images from the same client are regrouped into a single folder labeled as follow: ID-Gender, where "ID" is a 3 digits number that stands for client's ID and "Gender" stands for client's gender which can be "M" or "F" ("Male" or "Female").
Two different folders are provided "raw" and "roi". The "raw" stands the full palm vein image captured by the sensor and the "roi" stands the region of interest generated by the sensor in the acquisition process.
The format of the images is PNG.
Size of the images is 480 x 680 pixels.
Size of the files is around 165 kbytes per images.
* Example of the nomenclature fot the client #29:
* 029-M/029_L_1_1.png
* 029-M/029_L_2_1.png
* 029-M/029_R_1_5.png
* 029-M/029_R_2_5.png
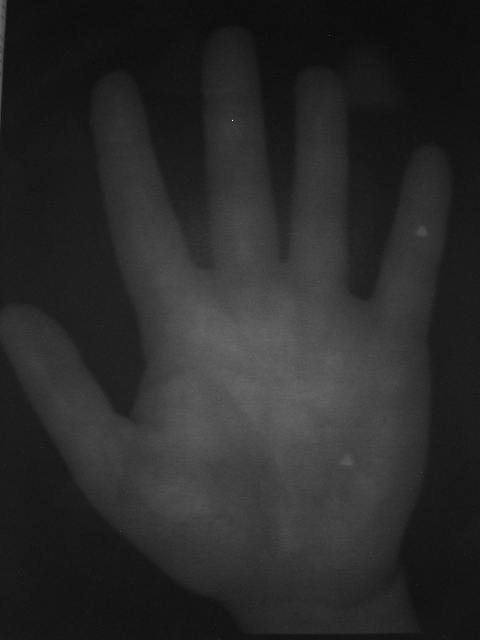
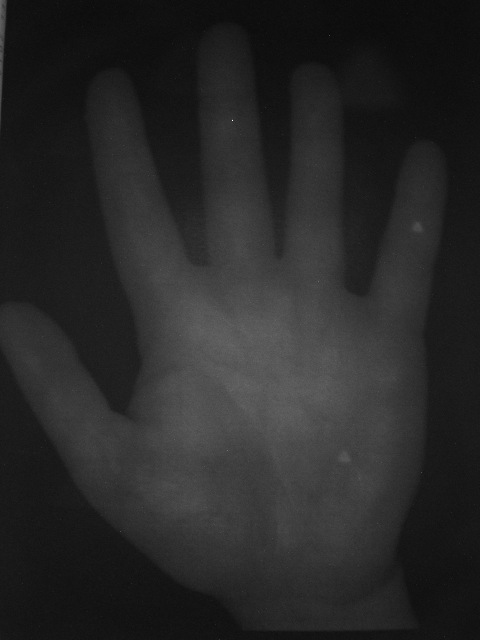
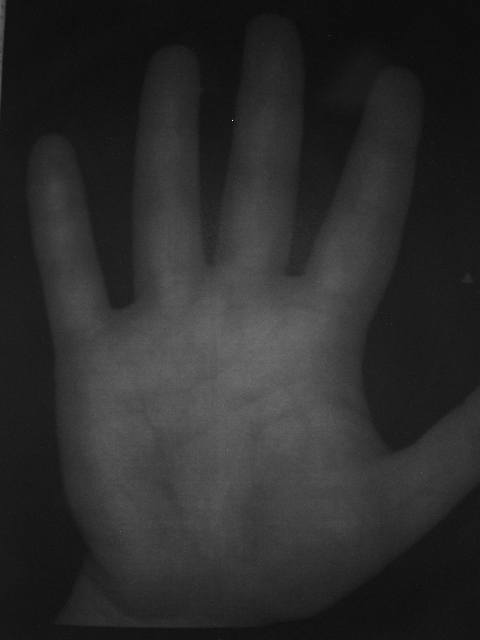
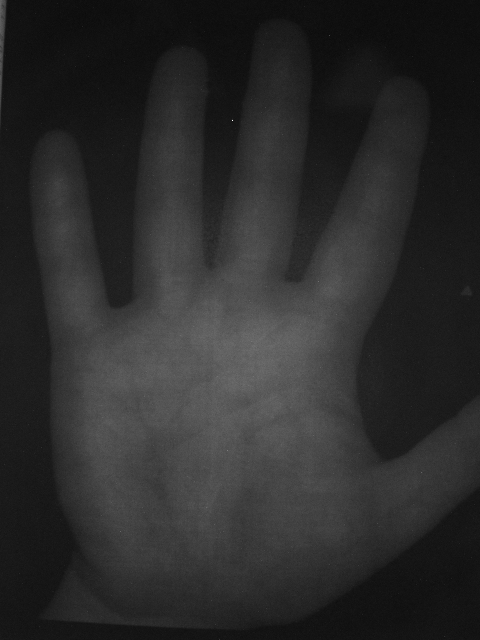
Here is an example of images from the database:
Database Protocol
The 1000 palmvein images from the 50 first clients from the Idiap Research Institute VERA Palmvein Database have been printed and presented to the sensor to record the 1000 images of the Idiap Research Institute VERA Palmvein Spoofing Database.
The precise protocol for elaborating the spoofing palmvein images is as follows:
1. Reshape to 380 x 525
1. Pre-processing the raw images using histogram equalisation and adding a padding array 50 black pixels
2. Printing at real palm size the pre-processed images on a thick 80 g/m2 white paper
4. The sensor leds are recovered by layer of 100 g/m2 white paper to attenuate intensity
5. The paper attack is presented to the sensor and recorded.
For more details, please check the paper cited below.
Reference
If you use this database, please cite the following publication:
Pedro Tome and Sébastien Marcel, "On the Vulnerability of Palm Vein Recognition to Spoofing Attacks", IAPR International Conference on Biometrics (ICB), 2015
10.1109/ICB.2015.7139056