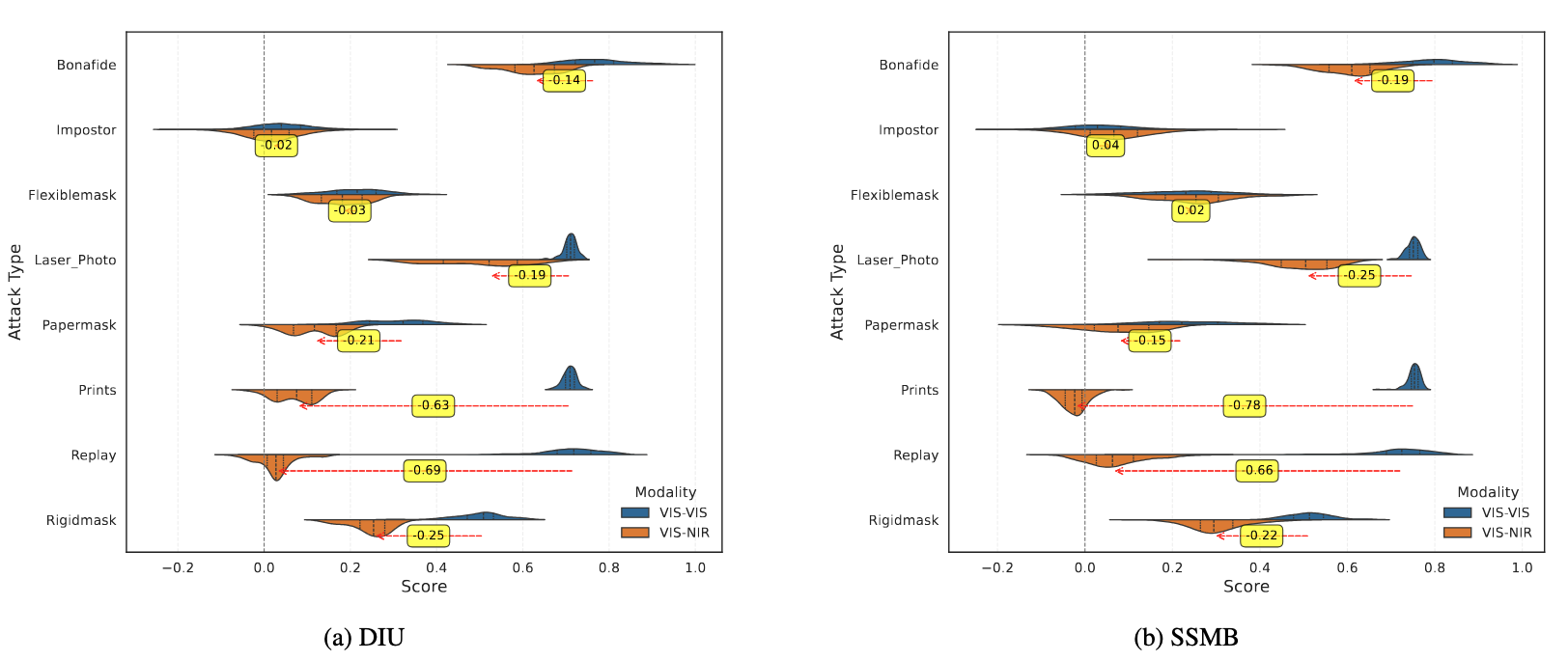
The score-distribution plots show that moving from a VIS-VIS to a VIS-NIR setting generally weakens presentation attacks: for most spoof categories, replay videos on tablets, ink-jet prints, masks and wearable disguises the median similarity score shifts left, reflecting the fact that their visual cues either disappear or lose contrast in NIR light. As a result, these attacks pose far less risk to cross-spectral face recognition than they do to conventional VIS-VIS systems. The outlier is the laser-printed photo attack: because laser toner is highly reflective in the NIR band, its score distribution shifts right, making it the most effective remaining threat under the VIS-NIR protocol
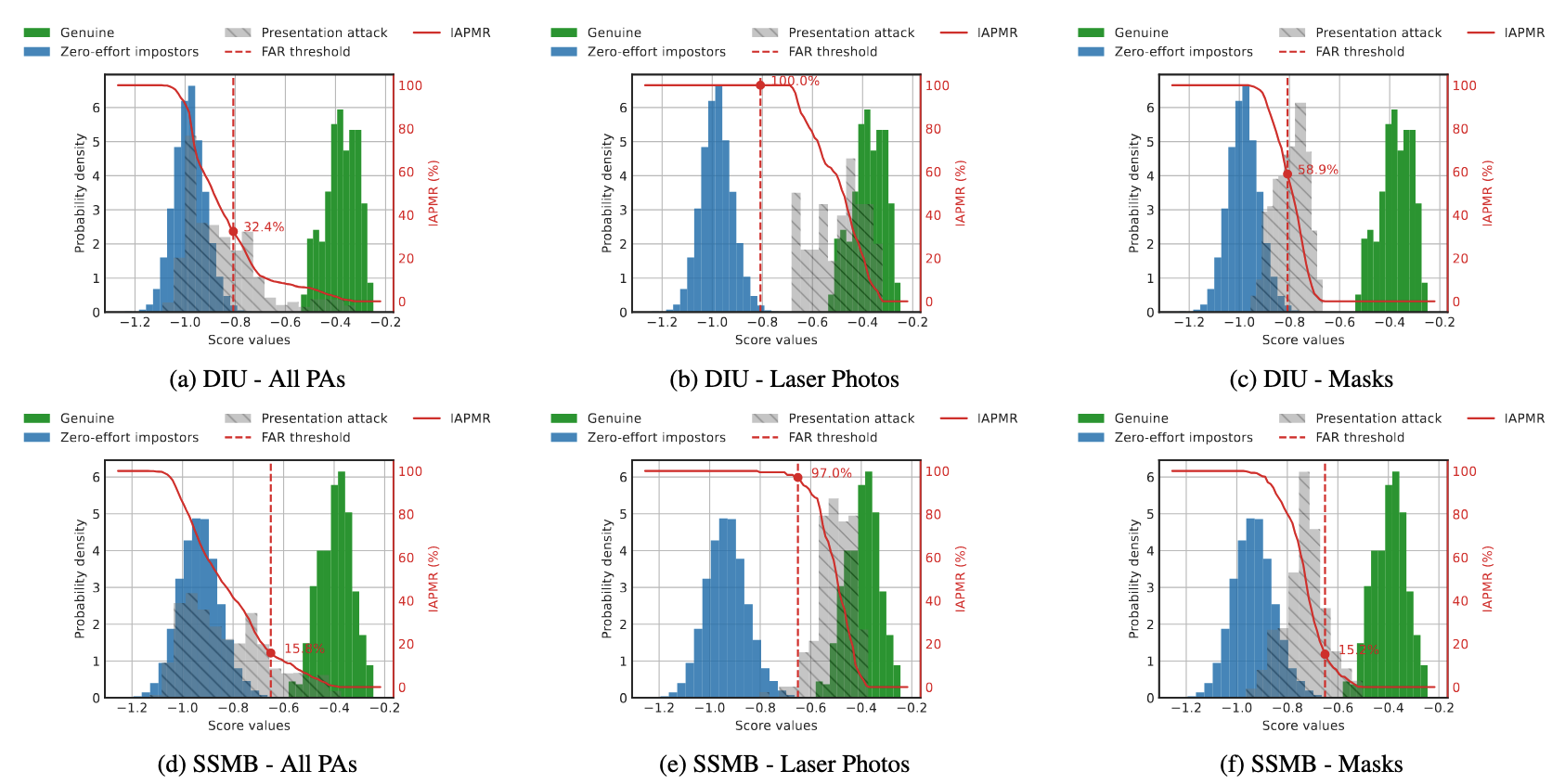
The histograms show how each powerful spoof type scores against two cross-spectral face-recognition models when VIS enrolments are probed with NIR images. Most attacks (masks and the mixed “All PAs” set) lie well to the left of the genuine-user curve and below the 0.1 % FMR threshold, signalling that they are rarely accepted. In contrast, the laser-printed photo curve rides almost on top of the genuine distribution and crosses the decision threshold, which drives IAPMR values up to 97–100 %. This tight overlap pinpoints laser prints as the single dominant vulnerability that survives the spectral gap.
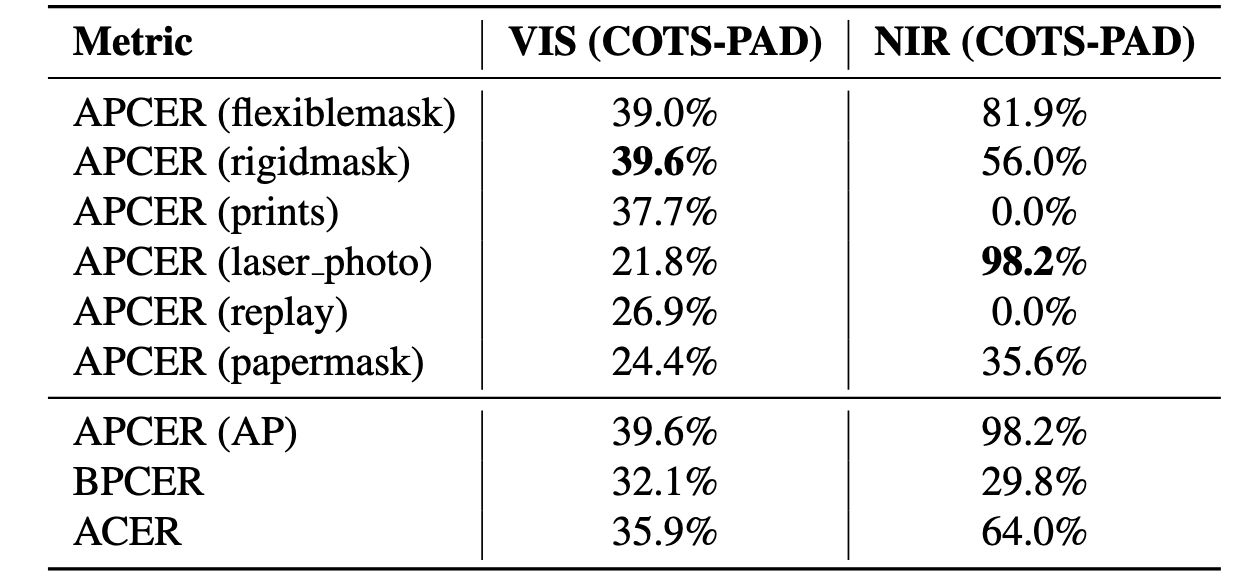
A commercial off-the-shelf PAD module, tested on the WMCA evaluation set, struggles to protect cross-spectral systems: when the PAD’s EER-based threshold is applied to probe samples, overall ACER remains high, especially in the VIS-NIR scenario, where laser-printed photo spoofs sail past detection with a 98 % APCER. VIS-VIS scores are somewhat better, but the sharp NIR drop-off confirms that generic COTS solutions are ill-equipped for heterogeneous face recognition and that purpose-built NIR-focused PAD is urgently needed.
The WMCA dataset used in this paper is publicly available at: https://www.idiap.ch/en/scientific-research/data/wmca .
@article{vulncfr,
title = {The Invisible Threat: Evaluating the Vulnerability of Cross-Spectral Face Recognition to Presentation Attacks},
author = {George, Anjith and Marcel, Sebastien},
booktitle = {2025 IEEE International Joint Conference on Biometrics (IJCB)},
pages = {1--10},
year = {2025},
organization = {IEEE}
}